After the power went out during the storm of (insert the worst storm you remember here), you swore you’d never be without power again. There was the ice-cold house, the frozen pipes, and all the other major inconveniences of living without electricity. You wisely invested in a home standby generator. Whether or not you’ve had to power up your generator during a winter storm since, you have the peace of mind knowing it’s ready to go when you need it. Or is it?
Like every mechanical system or equipment in your home, generator maintenance is necessary to ensure your generator is properly functioning. We’ve received emergency calls from homeowners who’ve had a generator installed, only to ignore it maintenance-wise and be left without electricity when it matters most.
Starting up a standby generator is more difficult when temperatures are below freezing. During fall in preparation for the cold weather and winter storms ahead is the best time to schedule a generator maintenance appointment. It’s easy to remember if you schedule it along with your fall furnace tune up and service.
If you don’t have a standby generator, now is the time to have it installed.
The Importance of Scheduled Standby Home Generator Maintenance
Standby generators are engines that create electricity to power your home’s essential systems in the event of a power outage. Like any other engine, a generator requires oil, filters, plugs, etc. A good analogy is a car. Just like cars aren’t designed to sit idle for months or years on end, neither is a generator. Like a car that has sat too long, a home generator is difficult, or even impossible, to start up.
During your standby generator service, your Envirotech technician will inspect your unit for damage, such as rust and unraveled wires. Oil level and lubrication is checked so that your generator can generate power efficiently and safely. Once everything is professionally checked, your generator will be ready for whatever this winter brings.
Easy Things You Can Do to Maintain Your Home Generator
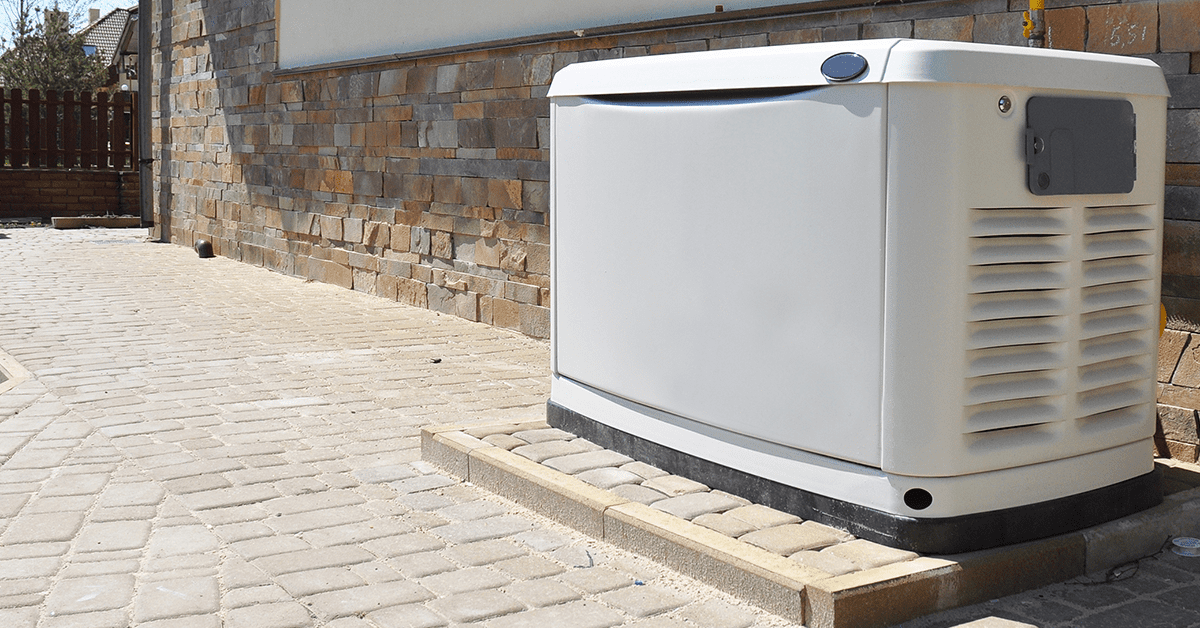
Anytime you’re outside doing yardwork, clear away leaves, weeds, and dead grass from the area surrounding your home’s standby generator to help keep the vents clear. Do this often in the fall when the leaves are falling because any blockage around the vents could cause your generator to overheat and shut down. Your standby generator requires proper airflow to operate. Plus, clearing vents helps minimize the risk of small debris being sucked into the unit and damaging internal parts.
When the snow begins to fall, remember to clear a path to your standby generator. Brush off any snow and ice that has accumulated and be sure to double check that the vents are clear of anything that would block airflow.
Take a “hope for the best, prepare for the worst” attitude when it comes to standby generator supplies. Make sure you have enough oil and gas on hand to keep the generator running for a few weeks. Our generator maintenance experts can show you what you need to know about oil levels and changes. Quick tip; keep extra spark plugs on hand even if yours are in good condition.
Don’t Compete with Emergency Calls in the Middle of a Winter Storm
During a winter power outage, the only thing worse than not having a home standby generator is having one that doesn’t operate. During winter storms all Kansas City HVAC companies are swamped with emergency calls. Don’t wait to schedule your generator maintenance appointment. We have appointments available now for both furnace and standby generator service.
We prefer and recommend Generac generators. Count on us for quality parts, installation, and services related to the trusted Generac name.